IT News
Protecting the IT Landscape in a Borderless World
The evolution of technology has pushed the perimeter of organisations further and further towards the edge, and we no longer have the monolithic structures we did in the past. The cloud, the Internet of Things (IoT), even the COVID-19 pandemic accelerating the adoption of a work from home model, have contributed to what has, in effect, become a borderless world. This means that the traditional approach to security of locking down the perimeter is simply no longer enough. The perimeter cannot be easily defined, and the way in which we access services has fundamentally changed. Cybersecurity mesh has emerged as a framework to address this challenge, with a distributed security architecture that more effectively meets the challenges of today’s landscape. Trust no one With IT infrastructure so...
Why Reimagined IT Strategies are Mission Critical for SMEs
Image sourced from IT Web Small and medium enterprises (SMEs) have been severely affected by the pandemic – many of which are struggling to ensure continuity, let alone achieve sustained growth. However, the news is not all negative. We have also seen countless examples of entrepreneurs rising to the challenge and tackling the unexpected head-on. SMEs who move quickly to take advantage of new technology business models are not only keeping afloat but are actually thriving. According to an article by the World Economic Forum (WEF), SMEs make up 90% of formal businesses in South Africa. These businesses contribute 34% to the country’s GDP and employ up to 60% of the labour force. For this reason, it is crucial that these small businesses continue to embrace technology and digital solutions i...
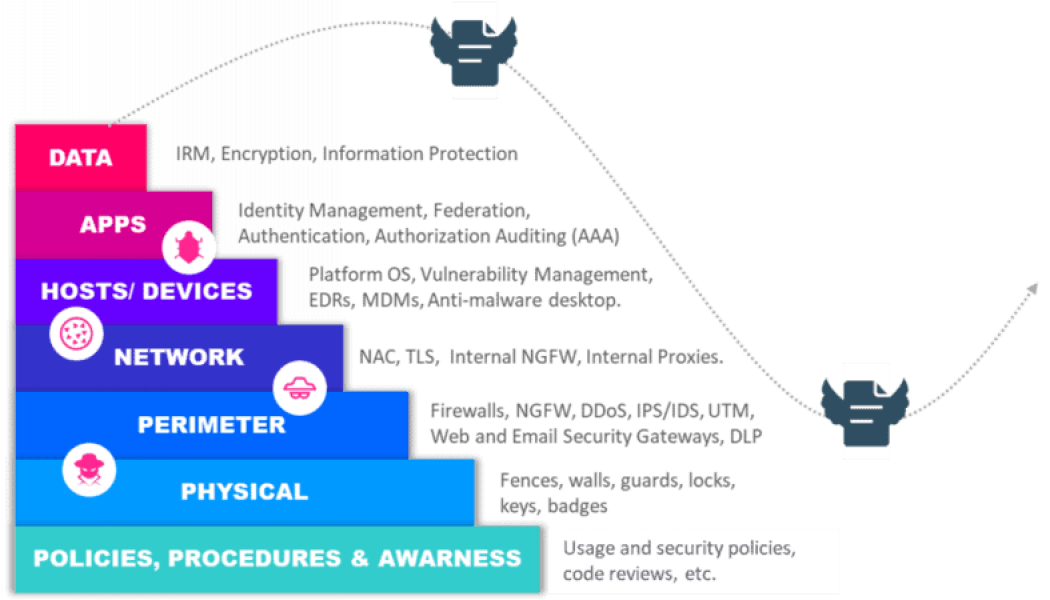
Fixing Your Cybersecurity Issues 1 Next-Gen Firewall at a Time
Stefan van de Giessen, General Manager: Cybersecurity at Networks Unlimited Africa When did you last check your firewalls as a barrier to entry against cybercriminals? And, perhaps more importantly: does your organisation still rely on a legacy firewall, or has it upgraded to a next-generation firewall (NGFW)? And have you considered the ‘Broken window’ principle when looking at your internal cybersecurity posture, in order to have a positive effect on your business processes? These questions are posed by Stefan van de Giessen: General Manager: Cybersecurity at Networks Unlimited Africa, who says, “The broken window theory rests on the idea that a neighbourhood or community that appears to be orderly and well-kept will be less susceptible to crime. Conversely, one that has many broken wind...
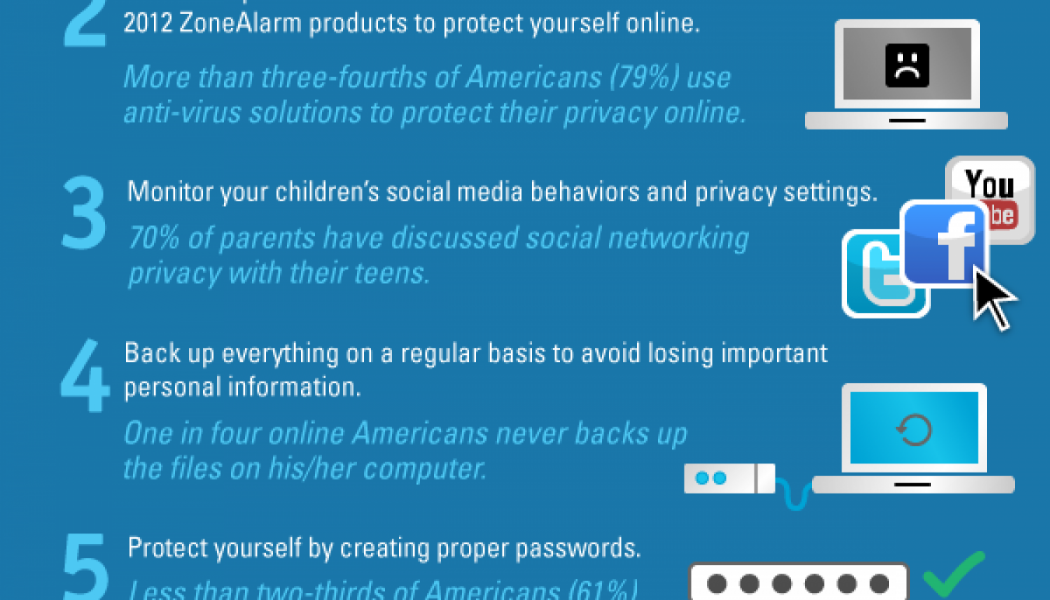
5 Reasons Why (Not Only) Financial Companies Struggle with Cybersecurity
Financial services companies have been a popular target for cybercriminals for a long time. Not without good reason, since beyond working with money, financial companies handle a slew of sensitive client data that criminals utilise in various fraud schemes or sell-off on dark web bazaars. According to Verizon’s 2020 Data Breach Investigations Report, in the past year alone the financial industry has suffered more than 1,500 incidents, with 448 confirmed data disclosures. Carey van Vlaanderen, CEO of ESET says that in addition to the long-standing threats, most companies have had to contend with the rapid transition to remote work. “The shift happened on extremely short notice, leaving companies with little time to deploy adequate cybersecurity measures or to prepare employees for looming c...
Paratus Zambia Introduces New Unlimited Internet Deals for Businesses
Image sourced from Patriot Paratus Zambia has introduced a new range of Infinity business deals. The telco says that these packages have been designed to give business customers access to more affordable and unlimited connectivity in Zambia, a market where a quality affordable internet connection is difficult to obtain. “We have created these Paratus Infinity packages because we fully understand how important it is for businesses to have access to quality unlimited connectivity,” says Paratus Zambia Country Manager, Marius van Vuuren. “We do not cap or shape our connectivity solutions because we know that our customers need to be always online to do their business.” The Infinity packages give customers access to uncapped and unthrottled data without dips in service quality or speeds due to...
Nutanix and CLC Africa Partner to Provide Digital Skills Across East Africa
Image sourced from Glassdoor Nutanix and Computer Learning Centre (CLC AFRICA) have joined forces to provide access to technical and sales skills across Kenya, Tanzania, Uganda, Ethiopia and Rwanda. The partnership is expected to help provide access to valuable certified digital training to a region where demand for hyper-converged and cloud solutions is growing. “As legacy environments come to their end-of-life, African businesses are rapidly upscaling their environments to software-defined environments based on hyper-converged infrastructure solutions that will ready them for the cloud,” says Rowen Grierson, Sales Director for Sub-Saharan Africa at Nutanix. “We are delighted to announce that CLC is now an official ATP for the region. Their experience in training, the quality of their ins...
Nutanix Appoints New Channel Director for Sub-Saharan Africa
Nutanix has appointed Andrew Gill as Channel Director for Western Europe & Sub-Saharan Africa (WEURSSA). Responsible for leading all channel and OEM activities in WEURSSA, Gill will oversee Nutanix’s go-to-market relationships with resellers, distributors, regional system integrators and technology partners in the region. Additionally, he will play a key role in driving channel-focused initiatives such as Nutanix Cloud Bundles, a strategic and unified offering to access Nutanix enterprise cloud software and solutions, while providing partners with greater value and autonomy through the sales channel. This unified management bundle enables Nutanix to expand access to its solutions, with an offering that meets the needs and budgets of any company as an essential addition to their En...