tech news
Synology Launches DSM 7.0 and C2 Cloud Expansion – Taking Data Management into Next-Gen
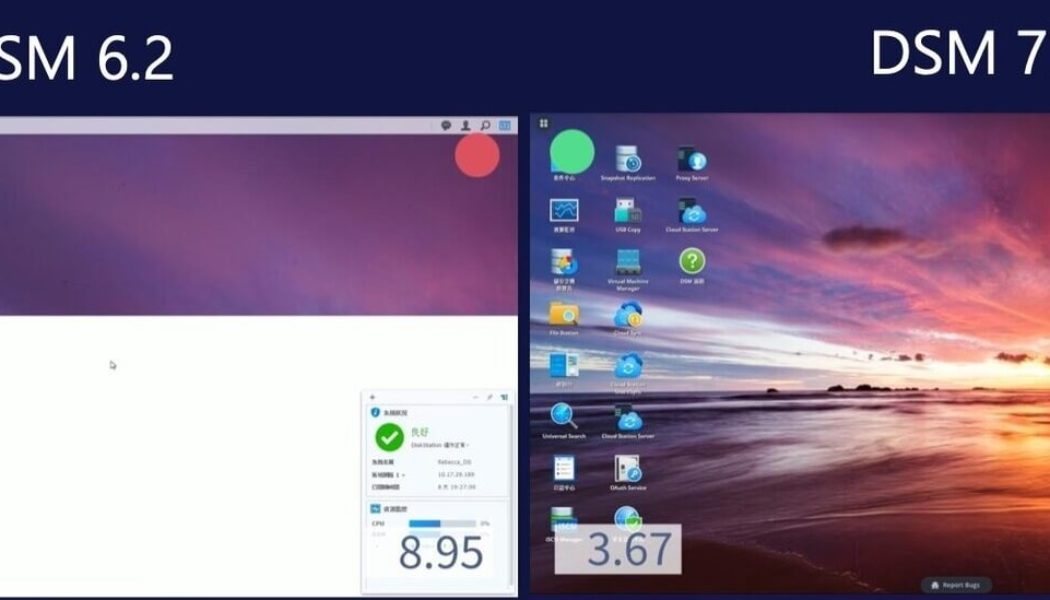
/* custom css */ .tdi_4_d6f.td-a-rec-img{ text-align: left; }.tdi_4_d6f.td-a-rec-img img{ margin: 0 auto 0 0; } Synology today announced the imminent release of DiskStation Manager (DSM) 7.0 and a massive expansion of the Synology C2 platform with four new cloud services. Focusing on enhancing security, system management capabilities, and improving data collaboration, DSM 7.0 is an enormous step forward for Synology’s NAS and SAN product lines. Building upon the success of C2 Storage, Synology is rolling out both hybrid and cloud-only products, including a new password manager, directory as a service, cloud backup, and secure file transferring solutions. Synology is heavily invested in expanding the availability of its cloud platform by starting work on opening a new data centre location t...
How AfChix and USAID Are Helping African Women Connect Their Own Communities to the Internet
Image sourced from AfrikaTech. AfChix – a network of African women in technology – is enabling women in rural Kenya, Senegal, Namibia, and Morocco to take the lead in connecting their communities to the internet for the first time. The organisation is one of the winners in the third round of the WomenConnect Challenge, funded by the United States Agency for International Development (USAID). The WomenConnect Challenge WomenConnect is a global call for solutions to improve women’s participation in everyday life by meaningfully changing the ways women access and use technology. As a winner in the first round of the WommenConnect Challenge, launched in 2018, AfChix has already built four community networks by installing communications infrastructure in rural areas. AfChix trains local women t...
Broken Endpoints in Your Organisation’s Cybersecurity: The Role of Superior Endpoint Detection
Stefan van de Giessen, General Manager: Cybersecurity at Networks Unlimited. Networks Unlimited is applying a ‘broken window, broken business’ principle when looking at an organisation’s internal cybersecurity posture, in order to have a positive effect on its business processes. The moral of the ‘broken window’ story, which has been studied by psychologists, is that once a window in a building is broken, people then feel that they are able to damage the property even further, and ultimately loot and steal from it, with impunity. “When we put this into a cybersecurity context,” says Stefan van de Giessen, General Manager: Cybersecurity at Networks Unlimited, “this means, in essence, making sure that you have no ‘broken windows’ or gaps in your security through which uninvited elements coul...