technology news
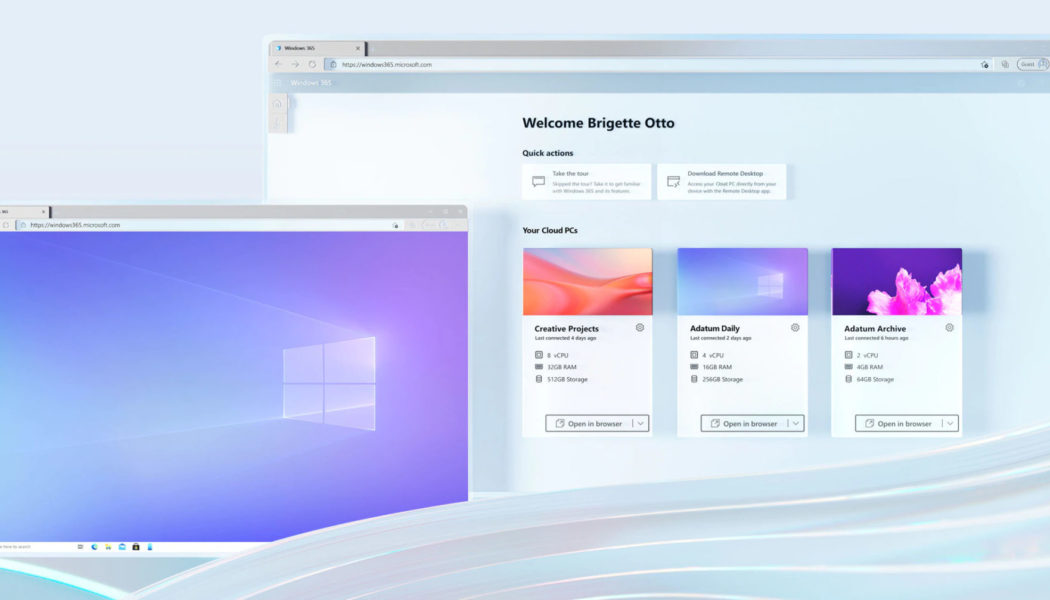
Why A Future-Proof Data Centre Environment is Key to Digital Transformation
Image sourced from Capacity Media. According to a recent report, Africa needs 700 data centre facilities to meet the growing demand for capacity and density in today’s digitally-driven operating environment. This is easier said than done given the power, land, and water requirements of modern data centres. And yet, this has become a non-negotiable at a time when cloud adoption has accelerated and become a top business priority. “These mission-critical facilities require resilient infrastructure to ensure uninterrupted services that enable business, operations, and systems to function effectively and continuously – especially given the ongoing lockdown conditions still experienced in many African countries, but for a post-pandemic future too,” says Peter Hodgkinson, Managing Director, WSP, ...
ICT Veteran Joins NEC XON as Executive VP
We use cookies on our website to give you the most relevant experience by remembering your preferences and repeat visits. By clicking “Accept All”, you consent to the use of ALL the cookies. However, you may visit “Cookie Settings” to provide a controlled consent. You Deserve to Make Money Even When you are looking for Dates Online. So we reimagined what a dating should be. It begins with giving you back power. Get to meet Beautiful people, chat and make money in the process. Earn rewards by chatting, sharing photos, blogging and help give users back their fair share of Internet revenue.
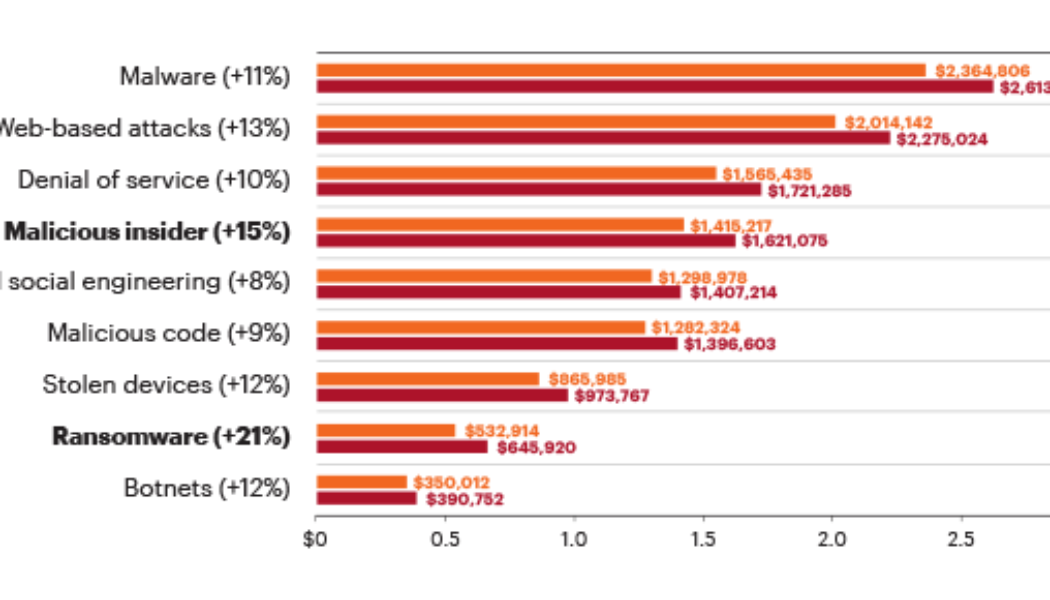
The High Cost of Cybercrime is Getting Higher
Image sourced from Finance Times. If cybercrime organizations could be publicly traded, we’d have an instant new multibillion-dollar industry sector. Indeed, cyber threats have become so pervasive that U.S. President Joe Biden recently signed an executive order aimed at improving federal cybersecurity in the wake of multiple significant cyberattacks, including the ransomware attack that shut down the Colonial Pipeline. Meanwhile, a broad coalition of experts in the industry, government, law enforcement, civil society, and international organizations have joined together in the Ransomware Task Force to build a framework for combatting ransomware. Ransomware attacks are only one method, however. Threat actors also use distributed denial-of-service (DDoS) attacks to ratchet up the p...