tech news
HMI – How People, Processes and Technology Work Together
When embarking on an industrial digitisation project, it’s important to consider how people, processes, and technology will work together. These three considerations are integrated in a somewhat symbiotic manner, which is why each should function optimally and compliment the other. A good example is IIoT; the technology promises secure access to a lot of data but is this data providing the right insight to people as opposed to burying them under a heap of information? Also, how do you ensure insights are delivered to workers whenever and wherever they need them, such as on the plant floor where they are working around production equipment. HMIs and Industrial Automation Enter Human-Machine Interfaces (HMIs); a technology developed to replace hard-wired pushbuttons and indicator lights with...
SA’s Zapper Launches Tap-On-Phone Payments
We use cookies on our website to give you the most relevant experience by remembering your preferences and repeat visits. By clicking “Accept All”, you consent to the use of ALL the cookies. However, you may visit “Cookie Settings” to provide a controlled consent.
Elon Musk Might Start Charging You to Embed or Quote Tweets
Elon Musk may be worth $246 billion, but he still took out loans to finance his $44 billion purchase of Twitter. In order to secure the cash, Reuters reports the mogul pitched banks a multitude of strategies to cut costs and make more money for Twitter, including reducing executive salaries and charging a fee for embedding and quoting tweets. Musk secured $13 billion in loans against Twitter and a $12.5 billion margin loan tied to his Tesla stock. In his proposal to lenders, the businessman argued that Twitter has a lot of room to make more money, pointing to a gross margin that ranks much lower than competitors like Facebook and Pinterest. In order to play catch up, Musk proposed profiting off of Twitter’s penchant for spreading both viral memes and important information by charging third...
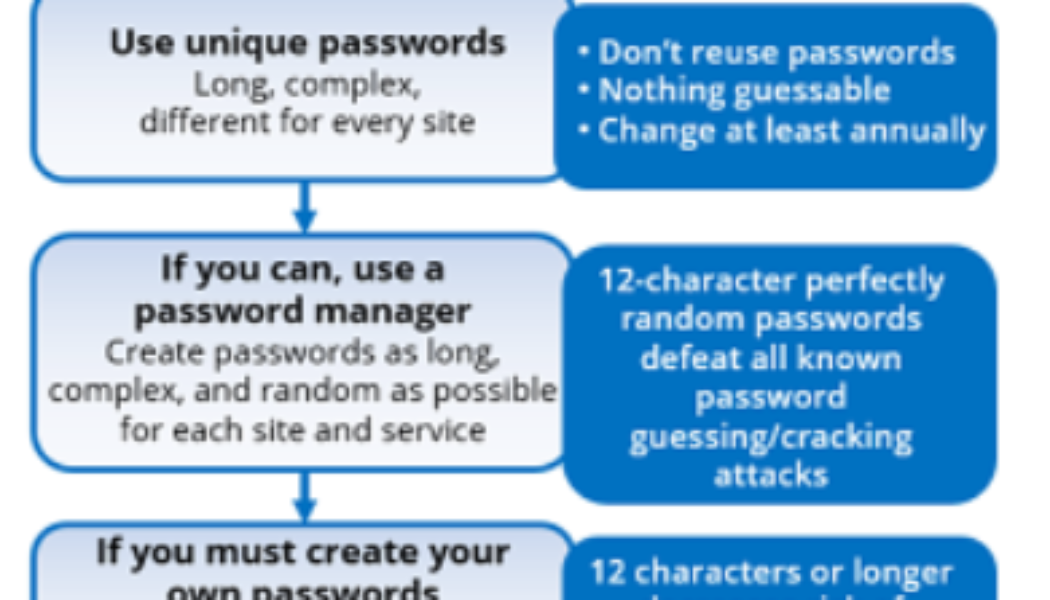
How Hackers Get Your Passwords & How to Defend Yourself
Sourced from Travellers Despite the world’s best efforts to get everyone off passwords and onto something else (e.g., MFA, passwordless authentication, biometrics, zero trust, etc.) for decades, passwords have pervasively persisted. Today, nearly everyone has multiple forms of MFA for different applications and websites AND many, many passwords. The average person has somewhere between three to seven unique passwords that they share among over 170 websites and services. And, unfortunately, those passwords often get stolen or guessed. This is why I recommend the following password policy guide: Most computer security experts agree with these policy recommendations, but more than a few readers might be shaking their heads, especially at the recommendations to use 20+ character passwords/pass...