tech news
Elon Musk Might Start Charging You to Embed or Quote Tweets
Elon Musk may be worth $246 billion, but he still took out loans to finance his $44 billion purchase of Twitter. In order to secure the cash, Reuters reports the mogul pitched banks a multitude of strategies to cut costs and make more money for Twitter, including reducing executive salaries and charging a fee for embedding and quoting tweets. Musk secured $13 billion in loans against Twitter and a $12.5 billion margin loan tied to his Tesla stock. In his proposal to lenders, the businessman argued that Twitter has a lot of room to make more money, pointing to a gross margin that ranks much lower than competitors like Facebook and Pinterest. In order to play catch up, Musk proposed profiting off of Twitter’s penchant for spreading both viral memes and important information by charging third...
How Hackers Get Your Passwords & How to Defend Yourself
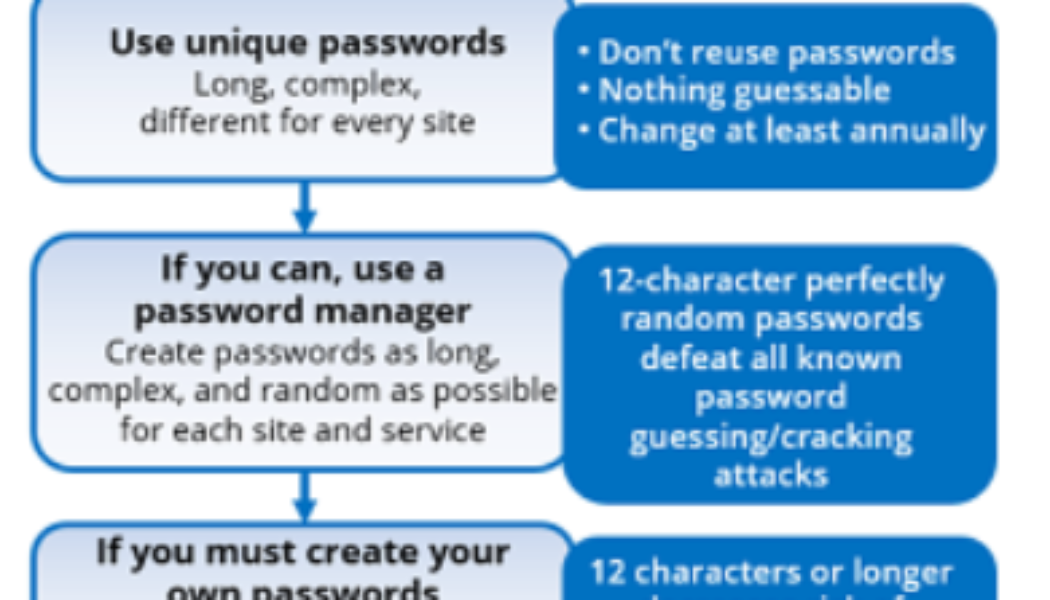
Sourced from Travellers Despite the world’s best efforts to get everyone off passwords and onto something else (e.g., MFA, passwordless authentication, biometrics, zero trust, etc.) for decades, passwords have pervasively persisted. Today, nearly everyone has multiple forms of MFA for different applications and websites AND many, many passwords. The average person has somewhere between three to seven unique passwords that they share among over 170 websites and services. And, unfortunately, those passwords often get stolen or guessed. This is why I recommend the following password policy guide: Most computer security experts agree with these policy recommendations, but more than a few readers might be shaking their heads, especially at the recommendations to use 20+ character passwords/pass...
Which African Country Will Adopt Bitcoin as Legal Tender Next?
We use cookies on our website to give you the most relevant experience by remembering your preferences and repeat visits. By clicking “Accept All”, you consent to the use of ALL the cookies. However, you may visit “Cookie Settings” to provide a controlled consent.
Kenya’s Cellulant Partners Tanzanian Fintech NALA for Overseas Payments
We use cookies on our website to give you the most relevant experience by remembering your preferences and repeat visits. By clicking “Accept All”, you consent to the use of ALL the cookies. However, you may visit “Cookie Settings” to provide a controlled consent.
Omnis Security from NETSCOUT: Protect Your Network from the Threats You Can’t See
On 09 December 2021, the world was alerted to the Log4j vulnerability [CVE-2021-44228 aka Log4Shell]. It is likely that threat actors already knew about the vulnerability before this date, says Tom Bienkowski, NETSCOUT Product Marketing Director, because it’s been reported that the vulnerability had been exposed much earlier in Minecraft chat forums. How does Log4j work – and what lessons does it bring? Log4j, which is open-source software provided by the Apache Software Foundation, records errors and routine system operations and sends diagnostic messages about them to system administrators and users. A common example of Log4j is when a user types in or clicks on a bad weblink and they receive a 404 error message. The web server running the domain of the attempted weblink sends a message ...
Why Organisations Need to Invest in Digital, Customer-Facing Technology
Image sourced from www.emediait.com Over the past two years, Chief Information Officers (CIOs) and senior IT executives have largely focused their efforts on digital transformation. This is mostly because COVID-19 forced organisations to expedite planned and unplanned re-engineering of their IT environments to fulfil the digital marketplace’s ever-increasing demand. While the top issues for IT departments have traditionally been (and continue to be) digital transformation, cybersecurity, data compliance, and cloud migration, customer experience has also become a top priority. This highlights the necessity to maintain a customer-centric mindset during digital transformation efforts, to increase customer retention, encourage repeat business, and grow revenue. Customer-centric digital transfo...
South Africa’s Dis-Chem Takes a Swing at WhatsApp Commerce
We use cookies on our website to give you the most relevant experience by remembering your preferences and repeat visits. By clicking “Accept All”, you consent to the use of ALL the cookies. However, you may visit “Cookie Settings” to provide a controlled consent.